NMSaaS Network Device Backup
* Automated Device Configuration and Command information backup in seconds
* Backup your running-configurations and startup-configurations
* Store as many historical backups as you need for as long as you want to keep them
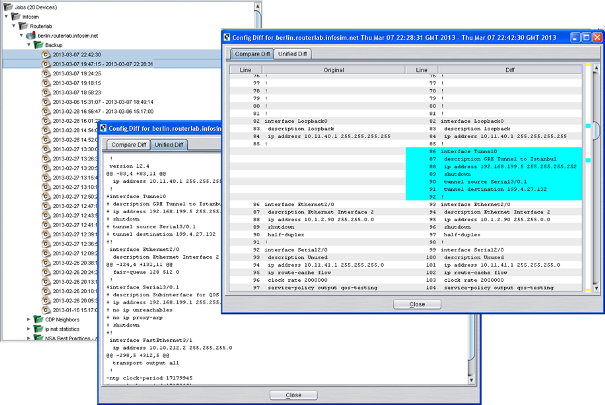
* Compare Backups to see changes from previous configurations
* Automatically backup configurations when a new change on the device is detected
* Retrieve and store “Show” commands in addition to traditional configurations
Contact Us
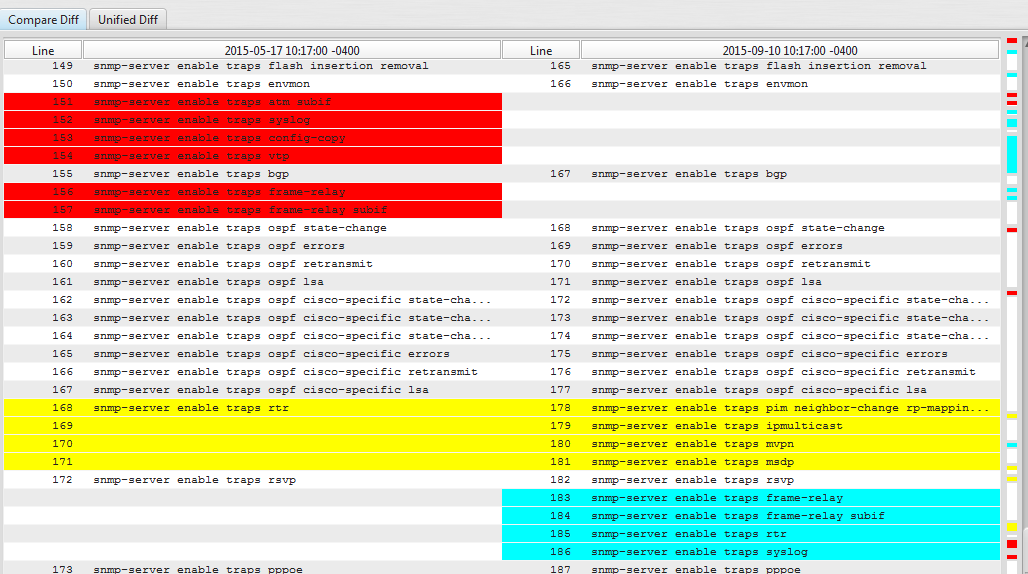
Our advanced backup engine will also automatically display any changes to the configuration backups over time. An easy to read “diff” view makes identifying changes simple.
NMSaaS Supports Most Major Device Vendors
With NMSaaS you can easily see the last configuration state (as well as older states) of your devices – including:
1. L2/L3 Switches 4. WLAN controllers
2. Routers 5. Network Visibility systems
3. Linux Servers 6. Firewalls
This module is a core component of any companies ITIL service and change management implementation. Using a powerful device scripting engine support for new devices can be enabled within the product quickly and easily.
Features
- Fully integrated module within the NMSaaS network management solution.
- Full device configuration backup and restoration through real-time change detection, manual request and scheduled processes.
- Extensible device interaction scripting enables rapid new device support.
- Device configuration change using simple CLI commands, advanced logic command snippets and templates.
- Intelligent configuration policy management using advanced logic snippets or scripts.
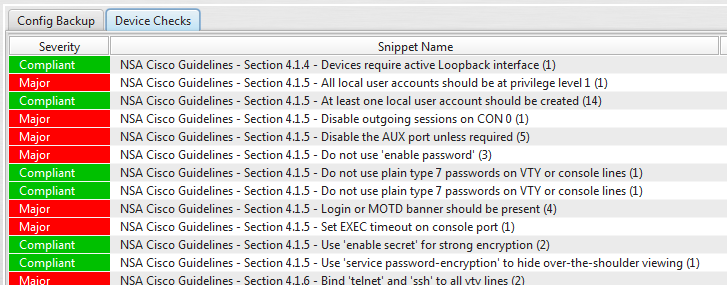
- Out-of-the-box security policy and remediation examples from the NSA best practice guidelines.
- Advanced multi-vendor device vulnerability identification and remediation.
Benefits
- Ensures a complete configuration backup for all devices under management.
- Historically version all configuration backups for easy restoration to previous known state.
- Automate complex tasks into simple templates.
- Accelerate time to complete changes and rollouts.
- Eliminate the risk associated with human error in the change process.
- Enforce corporate policies and quickly view configuration deviations from those standards.
- Ensure compliance with regulatory requirements such as Sarbanes-Oxley or Basel2 with a full audit trail.
- Enable the use of Best Practices within an organization such as ITIL v2/v3.
As the NMSaaS NCCM module captures every configuration change for a device within its database, the time to identify, analyze and rectify change related faults is greatly reduced as the operator is given the answers to the key questions of who, what, where and when. Historical device configurations can be used to restore devices to a previous known state with only a few mouse clicks.
Organizations can never truly eliminate the ad-hoc changes to network device configurations but with the NMSaaS NCCM module the impact of these changes can be mitigated. Larger scale changes can be structured into change process jobs for controlled execution and these changes can be rolled back at any time. Configuration changes can be made either using simple CLI commands or using more powerful logic based snippets and templates which enable less technical staff to make routine changes.
POLICY CHECKING
Key to managing device configurations is ensuring that they meet the corporate standards which can include, for example, security settings and software version requirements. The NMSaaS NCCM module allows these configuration standards to be built into policies that can be applied to devices and action can be taken if a device is in violation of these policies. Policies can be built using standard pattern matching techniques, advanced scriptlets for repetition checking and full script logic. This allows the user to create policies to cover even the most complex requirements using while-if-then-else logic to eliminate false-positives and false-negatives.
Powerful “snippet” based policy rules can be applied to any device or device group. Pattern matching algorithms will alert you when a policy has been violated.